IT security and data protection
Cyberattack techniques are evolving faster and faster and are becoming more sophisticated, destructive and unpredictable. Cybercriminals are rapidly discovering new areas of attack and departments responsible for business continuity and IT security have little time to react. In this environment, intrusion prevention systems based on artificial intelligence and machine learning, as well as aggressive patch management and threat intelligence solutions become imperative.
Dell EMC PowerProtect Cyber Recovery, from the Data Protection and Power Solutions family, is a state-of-the-art solution that isolates critical data from ransomware attacks and other advanced cyber threats. Based on machine learning, it identifies suspicious activity and accelerates and ensures the integrity of recovered data for a quick return to normal business operations.
Intelligent analysis tools and algorithms, full-context indexing and automated inspection allow you to determine if data has been “infected” with malware and apply remediation tools if needed.
Every organization, regardless of size or industry, is at risk of losing critical data due to cyber attacks. Under such conditions, a prevention strategy by monitoring storage systems for vulnerability to cyber threats will work well.
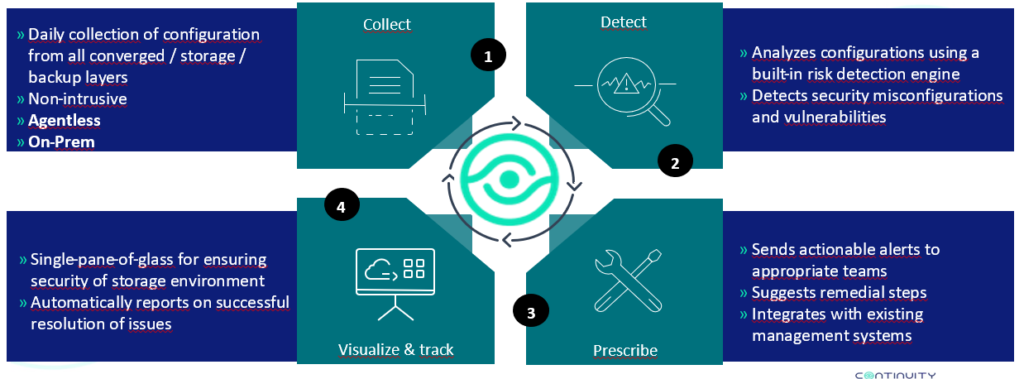
Array and SAN monitoring – StorageGuard (SG) – Continuity Software
This is a solution for managing the security status of storage and backup. StorageGuard scans and automatically identifies secure configuration issues and vulnerabilities in storage and backup security (Dell EMC and other vendors).
Key functionalities:
-Verifies configuration of authentication, authorization, encryption, protocols and services, audit logging, administrative access, and other areas.
-Uses a continuously updated knowledge base of vendor best practices for security configuration.
-Specifies and prioritizes risks, provides remediation guidance in accordance with vendor best practices and leading security standards (NIST, CIS, ISO, PCI and others)-across all areas of enterprise storage and backup.
-It is fully automated – built-in dashboard and reporting metrics.